This is what happens when we detect ransomware and what to do about it.
- According to Sophos’ commissioned survey of 5,000 IT managers, more than twice as many firms whose data was encrypted by ransomware restored it through backups. Almost 56% of the 94% organizations affected used this measure for remediating the ransomware attack.
- This is where Sophos Home comes in, about which we will talk next. Protection against ransomware, so that we can feel safe against any type of threat.
Ransomware Report: Sophos State of Ransomware Report 2020 The State of Ransomware 51% of organizations were hit by ransomware attack last year. And 73% of those attacks resulted in data being encrypted.
If you know a detection is a false positive, see Deal with false positives.
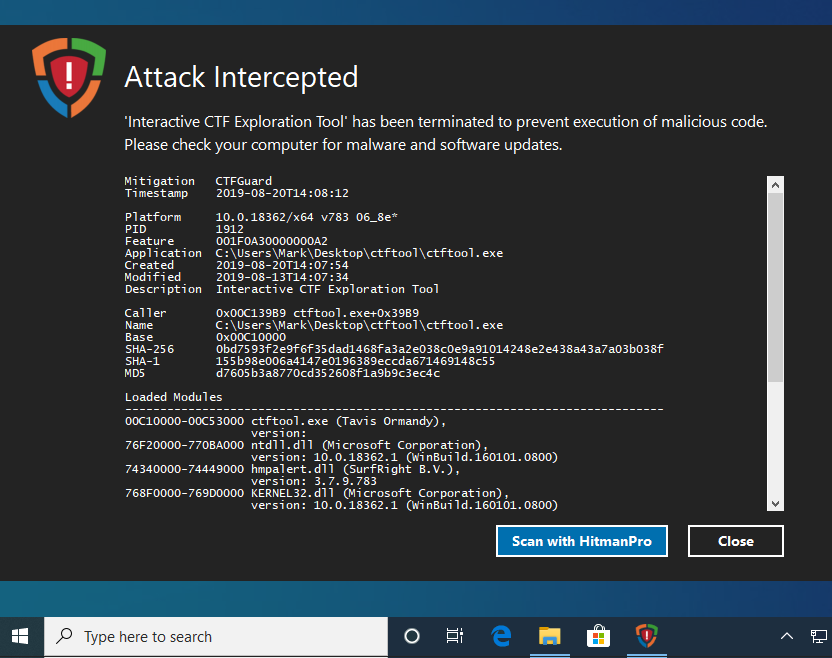
When we detect ransomware:
- We check whether it's a legitimate application like a file/folder encryption product. If it isn't, we stop it running.
- Files are restored to their pre-modification state.
- The end user is notified.
- A threat case is generated. This helps you decide whether to take additional actions.
- A scan starts to identify and clean up any other malware on the device.
- The device's health state returns to Green.
What to do if you see “Ransomware detected”
If you still need to clean up, do as follows:
- If automatic sample submission isn't enabled, send us a sample of the ransomware. We'll classify it and update our rules: if it's malicious, Sophos Central will block it in future.
- Move the computer temporarily to a network where it is not a risk to other computers. Go to the computer and run Sophos Clean (if it isn't installed, download it from our website).
You can run Sophos Clean on a server from Sophos Central.
- Go to Sophos Central, go to Alerts, and mark the alert as resolved.
What to do if you see 'Remotely-run ransomware detected'
We detected ransomware running on a remote computer and trying to encrypt files on network shares.
We have blocked write access to the network shares from the remote computer's IP address. If the computer with that address is a workstation managed by Sophos Central, and Protect document files from ransomware (CryptoGuard) is enabled, we clean up the ransomware automatically.
You need to do as follows:
- Find the computer where the ransomware is running.
- If the computer is managed by Sophos Central, make sure that Protect document files from ransomware (CryptoGuard) is enabled in the policy.
- If cleanup doesn’t happen automatically: Move the computer to a network where it is not a risk to other computers. Then go to the computer and run Sophos Clean (if it isn't installed, download it from our website).
- Go to Sophos Central, go to Alerts, and mark the alert as resolved.
What to do if you see 'Ransomware attacking a remote machine detected'
We have detected that this computer is trying to encrypt files on other computers.
We have blocked the computer's write access to the network shares. If the computer is a workstation, and Protect document files from ransomware (CryptoGuard) is enabled, we clean up the ransomware automatically.
You need to do as follows:
- Make sure that Protect document files from ransomware (CryptoGuard) is enabled in the Sophos Central policy. This provides more information.
- If cleanup doesn’t happen automatically: Move the computer to a network where it is not a risk to other computers. Then go to the computer and run Sophos Clean (if it isn't installed, download it from our website).
- Go to Sophos Central, go to Alerts, and mark the alert as resolved.
It’s three weeks since the word HAFNIUM hit the news.
The word Hafnium refers to a cybergang who are said to focus on stealing data from pretty much anyone and everyone they can infiltrate, across an eclectic range of industry sectors, and this time they hit a sort-of cybercrime jackpot.
The Hafnium crew, it turned out, not only knew about four zero-day vulnerabilities in Microsoft Exchange, but also knew how to exploit these bugs reliably in order to walk into unprotected networks almost at will.
The Exchange bugs didn’t include a remote code exeution (RCE) hole to give the crooks the direct and immediate access to a compromised server, but the bugs did allow the crooks to rig up RCE using a trick known as a webshell.
Greatly simplified, the attack goes like this:
- Exploit the Exchange bugs to write a booby-trapped web file called a webshell onto a vulnerable server.
- Trigger the booby-trapped web page hosting the webshell to run a Powershell (or similar) command to download further malware, such as a fully-featured backdoor toolkit.
- Enter at will and, very loosely speaking, commit whatever cybercrimes are on today’s “to do” list.
Unfortunately, as we explained when this news first broke, the name Hafnium caused fourfold confusion:
- Although Hafnium is often written in ALL CAPS, it’s not an acronym, so it doesn’t stand for something specific that you can protect against and then stand down from.
- Although Hafnium refers to a specific cybergang, the zero-day exploits they were using were already widely known to other criminals, and working examples soon became available online for anyone and everyone to download and use, both for legitimate research and for launching attacks.
- Although Hafnium attacks were associated with Microsoft Exchange in media coverage, the attacks these crooks were carrying out once they got in were not specific to networks using Exchange. The cybercrimes they ultimately committed could be initiated in many other ways.
- Although Hafnium was associated with data exfiltration and thus with potential industrial espionage, intrusions via these Exchange bugs could lead to many other crimes, notably including ransomware attacks.
It’s the last of these issues that concerns us here, because the Sophos Managed Threat Response team recently investigated a number of cases in which networks that hadn’t been patched against the abovementioned Exchange bugs had been infiltrated and attacked by a strain of ransomware going by the dramatic name of BlackKingdom.
In case you’re wondering, the crooks variously refer to their own ransomware using two words, weirdly written Black KingDom, as well using one word, as we’ve written it here. (We’ll stick to BlackKingdom in order to make it clear that we are talking about a specific threat, in the same way that we might write WannaCry or TeslaCrypt.)
Sophos Ransomware Statistics
The bugs exploited in this case are now widely referred to as ProxyLogon, which is the popular name used to refer to attacks that start off by using the Exchange bug CVE-2021-26855, typically followed by using CVE-2021-27065 and perhaps CVE-2021-26857 and CVE-2021-26858. The name ProxyLogin is a better word to use than Hafnium if you’re specifically talking about an intrusion initiated by those bugs, because the name isn’t tied to any criminal gang, and doesn’t imply any specific reason for the attack.
How it works
If you’re after the low-level details of BlackKingdom, you’ll be glad to know that SophosLabs has published a technical analysis of the malware program that does the dirty work.
Read the Labs report if you want to find out exactly how the malware works, and to get indicators of compromise you can look for on your network and in your own logs.
Although BlackKingdom is not technically sophisticated, that’s cold comfort if it’s just scrambled all your files.
As SophosLabs put it:
[O]ur early analysis reveals that it is somewhat rudimentary and amateurish in its composition, but it can still cause a great deal of damage.
What it does
Like many families of ransomware, this one:
- Skips folders needed to keep Windows running, including ‘C:Windows’, ‘C:Program Files (x86)’, ‘C:Program Files’ and various folders under your ‘AppData’ directory. The crooks want to be sure you can still boot Windows, read their blackmail demand and get online to buy bitcoins to pay the extortion.
- Stops any SQL server processes running, if the malware has administrator level powers, thus unlocking your database files so that they can be attacked along with everything else.
- Scrambles files on all drives it can find, including mounted network drives and removable disks that were plugged in at the time.
- Overwrites files in place, so there are no temporary copies of your unencrypted files left behind. This makes it hard to restore files by using disk recovery or “undelete” tools.
- Chooses a new encryption key for each computer, so that the decryption key for one PC won’t work on another.
- Never saves the decryption key to disk, so that you can’t undelete or easily recover it later. The malware uploads the key from your computer to an online file storage service, where the crooks can later download it but you can’t.
- Pops up a blackmail demand when it’s done. The malware also writes a text file with the criminals’ demands in it to a file called
decrypt_file.TxT. - Deletes the Windows Event logs, if it can, making it harder and more time consuming to try to figure out exactly what happened afterwards.
The blackmail demand starts like this:
The amount demanded is $10,000 in Bitcoin for each computer attacked:
Whether or not the criminals behind this attack really are routinely stealing their victims’ files before scrambling them, we aren’t sure.
However, as you will see from the SophosLabs analysis, the ransomware program that produces this message was installed and executed using the ProxyLogon exploits, which allow remote crooks to implant and run almost any program they want.
So even if they didn’t steal all your data first, they almost certainly could have…
…and so could any other crooks who came across your unpatched servers before, during or after the BlackKingdom attack.
What to do?
Sophos Security Threat Report
- Patch early, patch often. If you are at risk of a BlackKingdom attack unleashed via the ProxyLogon exploits, then your network is as good as open for anyone to get in and do almost anything, at any time they want.
- Do your backups. That way you can recover from losing your data no matter how it happens. A simple memory aid is “3-2-1”, which means you should have at least three different copies (the one you are using now plus two or more spares), using at least two different backup systems (in case one should let you down), and with at least one copy stored offline and preferably offsite (where the crooks can’t tamper with it during an attack).
- Peruse your logs. Crooks don’t always succeed at their first attempt, so keep your eye open for signs that an attack may be under way.
- Consider an anti-virus with data scrambling protection. For example, Sophos endpoint products include CryptoGuard, which detects ransomware generically by how it behaves, not by what it looks like. If CryptoGuard spots what it thinks is a rogue file-encrypting program, it can not only step in to block the attack but also automatically reverse any encryption that’s happened so far.
By the way, there are a few peculiarities about the BlackKingdom malware that give you a small (though it may admittedly only be a very small) chance of recovering your data, even if you don’t have a backup, without paying the criminals for the decryption key.
So if you do end up as a victim of this attack, talk to someone you know and trust for advice before you rush into any ill-considered response.
If you have suffered any sort of cybercrime attack, including but not limited to ransomware, and you don’t have an IT partner of your own to turn to, the Sophos Managed Threat Response or Sophos Rapid Response team would be happy to hear from you.
Sophos Ransomware Survey
LEARN MORE: HAFNIUM EXPLAINED IN PLAIN ENGLISH
Sophos Home Security
Original video here: https://www.youtube.com/watch?v=xVasO4k-mMQ
Click the cog icon to speed up playback or show live subtitles.
